Updated: January 9, 2020 | | Tags: Active Directory, Code, Password, PowerShell, Script, Security
I created a powershell-script which will reset the password of all users in a specific Organizational Unit.
I prefer to set unique high-end passwords for all users. If you prefer a more ‘user friendly’ approach simply…
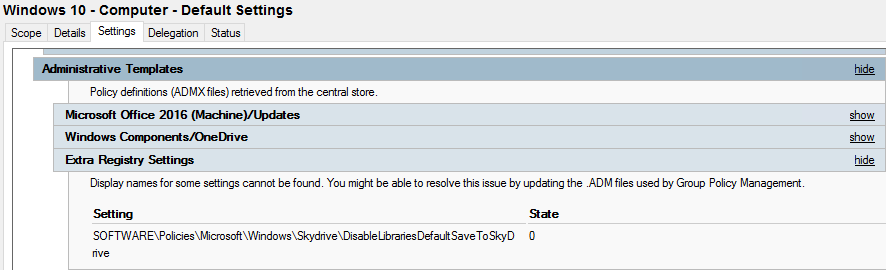
Posted: April 1, 2017 | | Tags: Active Directory, ADMX, GPO, OneDrive, PowerShell
A downside with the ADMX files is that when you update them, and the new files replace settings and values you end up with orphaned settings in your GPOs. In our example we had two orphaned registry values from a previous OneDrive ADMX.
Updated: November 12, 2017 | | Tags: Active Directory, GPO, PowerShell, Profile, usertile, VBs, Windows 10
We have been working on migrating a customer from Windows 7 over to Windows 10. Our goal is to have Windows 8 and 10 clients pull the pictures from Active Directory to the users local profiles.
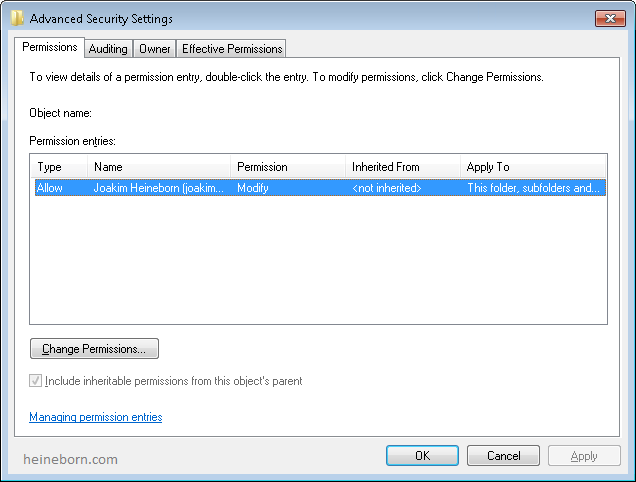
Updated: May 17, 2016 | | Tags: Active Directory, File and Storage Services, PowerShell, Script, Security
The script will look through the a selected Organization Unit and verify that all users have a Home Directory set, and that it has the appropriate NTFS permissions.
Previously all users had Full-permissions on their home folder, which led to the users resetting permissions and removing unwanted permissions (Backup or Admin accounts) to their “private” stuff.
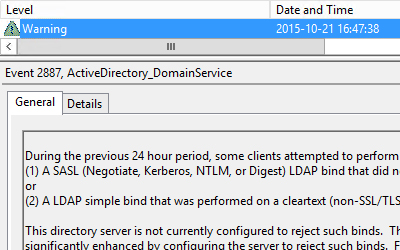
Updated: May 17, 2016 | | Tags: Active Directory, GPO, Security, Troubleshoot, Windows Server 2008, Windows Server 2012
I noticed that a couple of Domain Controllers started reporting Warning-messages. It turns out that one or more clients have been using LDAP binds that are performed on a clear text (non-SSL/TLS-encrypted) connection.
Updated: November 2, 2023 | | Tags: Active Directory, Azure AD, Azure AD Sync, Cloud, Entra ID, PowerShell, Troubleshoot
Depending upon the version of the sync solution that you are using to replicate directory data from on-premises Active Directory to Office 365 there are different commands that you will need to use.
Updated: November 2, 2023 | | Tags: Active Directory, Azure AD, Azure AD Sync, Entra ID, Troubleshoot, Windows Server 2012
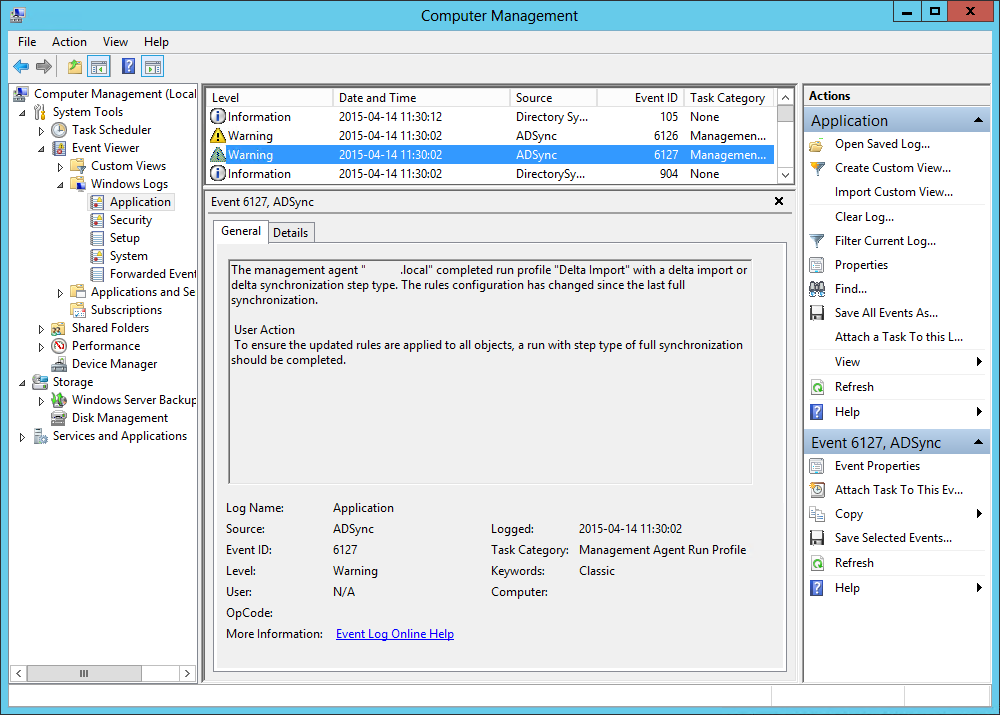
While doing a regular maintenance check on my customers servers when I came across a new event in the log.
I’ve previously wrote about changing the sync schedule on this server.
But today I noticed two event errors, ADSync event 6127 and 6127.
Updated: November 2, 2023 | | Tags: Active Directory, Azure AD, Azure AD Sync
I finally I got some time to play with the new Azure Active Directory Sync tool and its configuration.
The installation was very straight forward. The step-by-step instruction are provided on MSDN. The administration tools and scripts are located in difference places compared to DirSync which was little confusing in the beginning.
Updated: November 2, 2023 | | Tags: Active Directory, Azure AD, Azure AD Sync, Code, Entra ID, PowerShell, Troubleshoot
By default DirSync runs every three hours; which for some environments or during testing may not be frequent enough…
Updated: November 2, 2023 | | Tags: Active Directory, Azure AD, Entra ID, PowerShell, Script, Troubleshoot
You can install the Azure module directly from the PowerShell prompt and connect to the numerous services offered by Microsofts extensive cloud solution!